Understanding VPN and How to use it?
To send and receive a simple message goes a long way. The internet is a place, which has both the sides depending on the use. It can be safe or may not be. In this context, the VPN (Virtual Private Network) is one of the controversial topics that can contribute or hinder your security. Hence to make it simple we have build this guide on Understanding VPN and How to use it?
To access any website, app or just be connected to a network, various protocols, standards and technologies are required. VPN is something that many people use without knowing it and it is more present in our daily lives than we realize. Technology helps to improve network security, but can be dangerous at times.

There are many questions like,
- How can I use it to my advantage?
- When or not to use? Is free VPN safe?
- Can I only use paid services?
- What are the indications for using a paid VPN?
For all your quarries we have built this guide on Understanding VPN and How to use it?
What is VPN?
VPN is the acronym for Virtual Private Network. In a very summarized way, it is a set of private communications, built on a public network. For example: the public network would be the internet, while the private network would be access to Netflix. It is necessary to be connected to the network, but that is not enough. The user needs to access their own private account, which uses VPN, to “ensure the security of their account”.
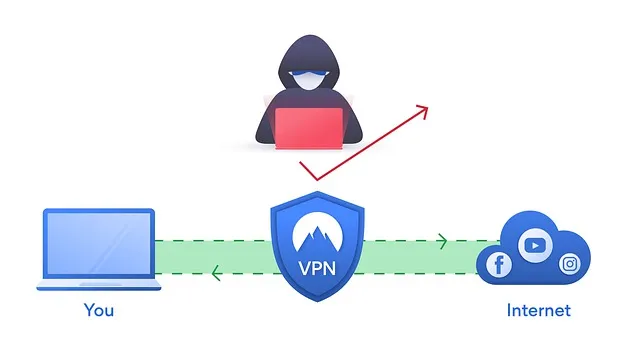
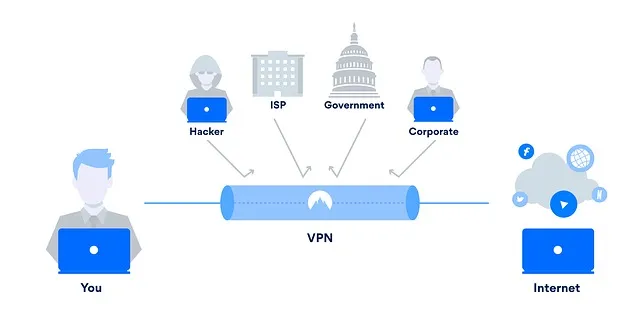
It is a secure and encrypted connection. However, data traffic continues to be carried over the public network, which is used with all traditional protocols and standards. Sometimes, this path may not be so safe and can be hacked with bad intentions. In this sense, the VPN is quite useful to secure this path, knowing exactly where it goes.
The great benefit of VPN is turning insecure networks into safe options for users. That’s because it uses encryption and tunneling (or tunneling) protocols. This phenomenon consists of encapsulating one protocol within another, allowing a packet to be sent securely over a public network. This makes them have greater authentication of data, going through processes of greater confidentiality and integrity of the information being transmitted through this “tunnel”.

Also, to establish this secure network, some protocols are applied. Some of the more common ones found on most VPN networks are listed below. These Protocols helps to enable a secure connection, meeting different types of needs.
- Layer 2 Tunneling Protocol (L2TP)
- L2F
- Point-to-Point Tunneling Protocol (PPTP)
- IP Security Protocol (IPsec)
Another important point is that VPN naming can only be assigned to remote access services. An example is the Remote Access Service, better known by the acronym RAS, which is found in Windows versions from 2000 onwards. Another option is the Secure Shell (SSH), available on GNU, Linux and other Unix variants.
VPN Types:
- Host-to-Network: Also called remote access, it can connect a single computer to a network.
- Site-to-Site: Connects a single computer to two networks.
VPN Benefits
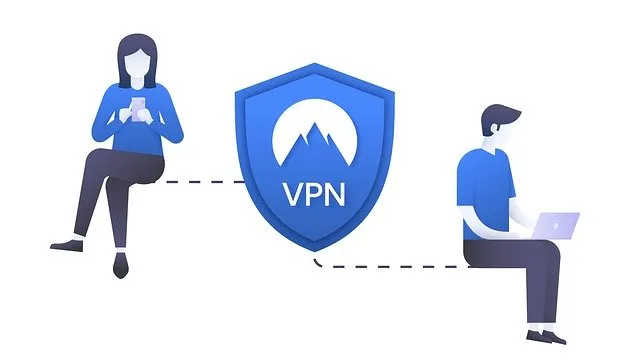
VPNs can be very useful in corporate environments, allowing employees to access data remotely. VPN services are highly used by companies, users who want extra protection, people who travel a lot and work with the internet or need it to perform their functions. That’s because it’s a best way to ensure that no matter which network you use, your connection will be secure.
It is common for users those who need to make multiple downloads on their computer. Some even prefer to use unusual systems to obtain services and in these cases, the use of VPN becomes even more recommended. Another common user profile is those looking for and performing illegal file installations.
How to use VPN?
Today, there are numerous options for companies that provide VPN services – both free and paid. It is necessary to be very careful when subscribing to this type of service.
In order to use VPN, a subscription is required. The service itself will offer the download to the user. After the installation, you need to choose which server to connect to and once you are connected its ready. Now any website, app or internet service you choose will automatically be redirected to the VPN.
It is possible to download it on mobile devices such as tablets and smartphones and on PCs. The user chooses and installs it on the devices he wants. Despite this, the most common is that they are done on notebooks and desktops.
VPN Services

By typing the acronym into Google, the user will be directed to dozens of websites and advertisements that indicate possibilities.
Is it enough?
Absolutely not!
When the user subscribes a VPN, whether it is paid or free, all information is sent to the servers of this service. Therefore before hiring a service, it is important to do a good research. Look for videos, testimonials and complaints from users who have already purchased this VPN. It is worth doing searches on social networks and asking for referrals to friends. Some of the most safe options are:
ExpressVPN
This is one of the most popular services available right now. It has good review score, according to the top 10 VPN website. You have to buy service, with 24/7 technical support. It currently has an active big community of users. It is available as an extension for Chrome and Firefox browsers.
CyberGhost
is also considered a high performance VPN, offering 24/7 support. It provides paid service and rated under top 10 VPN. It can give an option to connect to servers more than 90 countries. Works via browser extension for Chrome and Firefox.
Surfshark
Another option is Surfshark. Its a paid service, with the same support as mentioned. It promises to be an excellent solution for privacy needs without sacrificing speed. Easily works with extensions for Chrome and Firefox.
NordVPN
NordVPN promises to be a good balance between speed and privacy. It is also a paid option and offers the same full-time support. It is available for Chrome and Firefox and has a good feedback from its users.
HidemyASS
This is the option that promises to have “most server locations worldwide”. It is a paid tool, with full support and good review.
It is possible to notice that the most recommended services are also paid. In general, people rely more on services that require payments, whether monthly or annual, depending on each option.
Free VPN Services
Despite this, there are some free options that have good reviews. If you still want to make use of free services, use it at your own risk. The most recommended VPN services are paid.
It is worth noting that many of the paid versions offer free trial periods. If the user is afraid of not adapting to the service, or does not like the choice, you can cancel the subscription before the end of the free period (usually one month) and there will be no charge.
Free VPN Options:
- TunnelBear
- WindScribe
- VPN Gate
- hide.me
There are some other safe options that use VPN. Opera browser uses built-in VPN technology options, without the user having to register on another system. Obviously, if someone already uses their own service and wants to port it to their browser, they can do that without any problems.
“To activate the free VPN for the first time, enable it in Menu -> Settings -> Privacy -> VPN. From then on, you will see an icon in the address bar that shows the VPN status. Just click on it to activate and disable the VPN service. You will be able to select the desired virtual location and also see the statistics of the data used.
Opera VPN can also be used in private browsing windows.”
Is VPN really important?
VPN has many uses, especially in the business sector. Despite this, when some non-specialized user looks for this solution, it is quite common that it is to circumvent some system. The main one is access to streaming catalogs from other countries and to have greater access to available movies and series.

The uses are much greater and can be essential for the development of works. For a user who just wants to protect their data, make a more secure connection – but doesn’t have very sensitive information – Opera itself can meet the needs very well. Now, if there is a need for even greater protection, one of the many services available may be able to meet the security demand.
During the Covid-19 pandemic, several sectors of the industry were affected. Several companies started to do their work remotely and adapt to their needs. The use of VPN was one of those that registered a lot of increase in this period. That’s because, using technology, employees are able to connect to the company’s private network, even though they are geographically distant from it.
Using a VPN guarantees that all information will be encrypted and will not be interfered by hackers. This is an extra protection, which ensures more secure information. Despite this, it is worth some additional care, as we have already mentioned throughout this article Understanding VPN and How to use it?
Suggested Reading:
- 10 Command Prompt Hacking Tips
- How to identify phishing emails?
- What is DDoS attack and How it works?
- Different Types of Processor Socket in Motherboard
- SSL/TLS Vulnerability Fix for Nessus Scanner
Precautions when using a VPN
Nothing is free is this entire world. The profit that companies make from selling data is huge. This saying became very famous after the Cambridge Analytica scandal, when it was discovered that Facebook had been trading the information of its users for years.
Where does this apply for VPN? Let’s remember that the service has access to all user information to make it “safe”. However, some services may use this data to make their profit. So what you would use for greater security ends up having the opposite effect.
So, when hiring a VPN service – whether it’s paid or free, but even more attention to free services – it’s good to make sure that it really is a serious and safe option. Do research before subscribing to any service, watch videos and read comments from existing users for their feedback or review.
Summary
VPN is the acronym for Virtual Private Network, in free translation “Virtual Private Network”. It is a secure, encrypted connection built “on top” of the public internet network. VPN naming can only be assigned to remote access services. The most recommended VPN services are paid, but there are good free options. Hope you liked this guide on Understanding VPN and How to use it? Please do share with others.